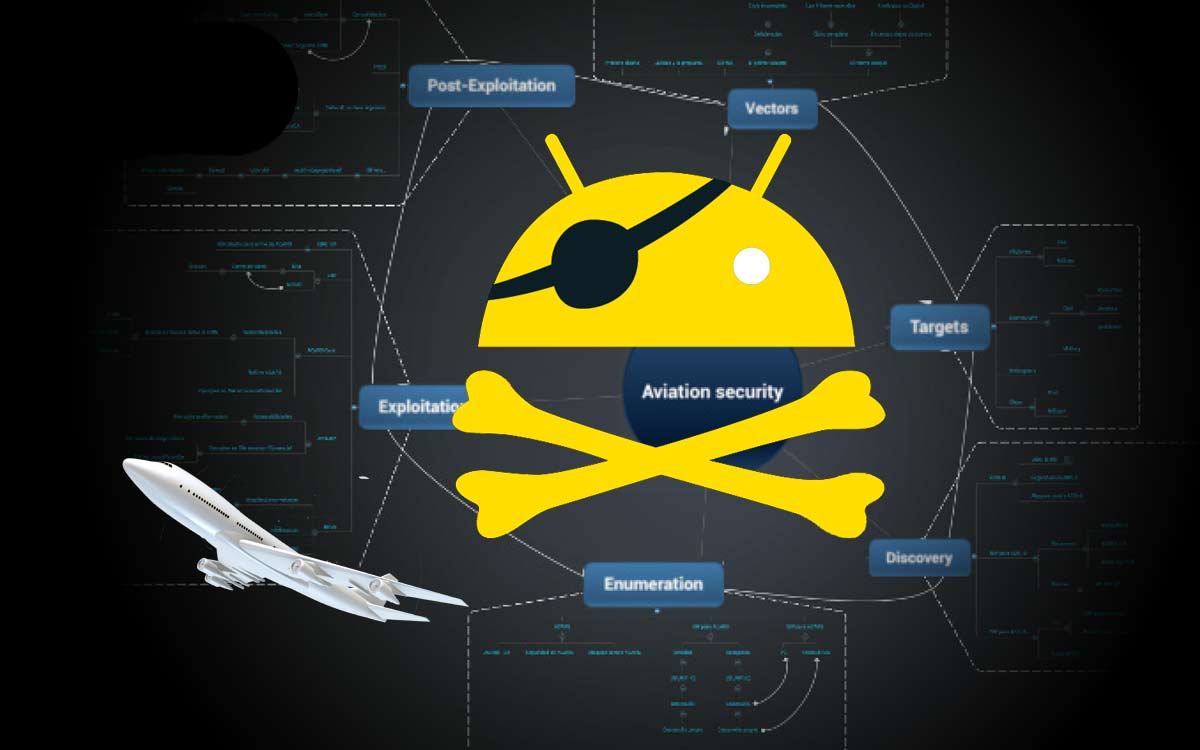
Hacker Proves He Can Hijack An Airplane Using An Android App, FAA Shocked
One of the main jobs that a security consultant is asked to do is find vulnerabilities. I’ve done security consulting before and the look on a clients face when you show them how vulnerable they are is a mix of embarrassment and appreciation. Recently, a topic has been trending online about a security consultant by the name of Hugo Teso, who claims he has created an Android app called PlaneSploit that would allow him to remotely attack and hijack commercial aircraft.
He recently presented his findings at the Hack in the Box security conference in Amsterdam where, among other things, he exposed the fact that a number of aviation and aircraft systems have no security in place.
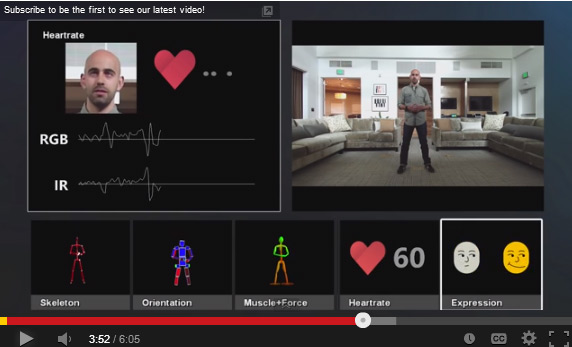
 Teso, a trained commercial pilot for 12 years, reiterated that the Automated Dependent Surveillance-Broadcast (ADS-B) is unencrypted and unauthenticated which can lead to passive attacks like eavesdropping or active attacks such as message jamming and injection. Furthermore, the Aircraft Communications Addressing and Reporting System (ACARS) – a service used to send text-based messages between aircraft and ground stations – also has no security.
Teso, a trained commercial pilot for 12 years, reiterated that the Automated Dependent Surveillance-Broadcast (ADS-B) is unencrypted and unauthenticated which can lead to passive attacks like eavesdropping or active attacks such as message jamming and injection. Furthermore, the Aircraft Communications Addressing and Reporting System (ACARS) – a service used to send text-based messages between aircraft and ground stations – also has no security.
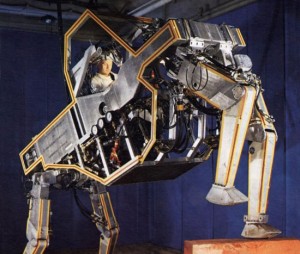
With these vulnerabilities in mind, he used virtual planes in a lab to demonstrate his ability to hijack a plane rather than attempting to take over a real flight as that was “too dangerous and unethical.” He used ACARS to gain access to the plane’s onboard computer system and uploaded Flight Management System data.
Once in, he demonstrated how it was possible to manipulate the steering of a Boeing jet while it was in autopilot mode. The security consultant said he could cause a crash by setting the aircraft on a collision course with another jet or even give passengers a scare by dropping down the emergency oxygen masks without warning.
A pilot could thwart an attack by taking the plane out of autopilot although he pointed out that several newer systems no longer include manual controls. Some systems could be updated to patch the vulnerabilities but many legacy systems would be difficult, if not impossible, to update.
Watch The Video Below & Tell Us Your Thoughts in the FB Comments.